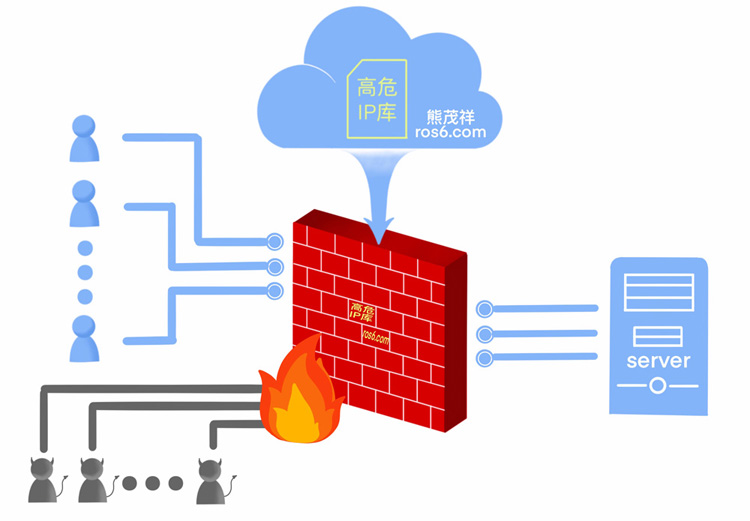
新建高风险IP库项目(公测)【跟着大神学走路】
更新时间: 2021/01/20
mikrotik导入例子/imp scaners.rsc
linux导入例子 iptables-restore < scaners.bak
:do [/tool fetch url="https://cache-1.oss-cn-beijing.aliyuncs.com/file/scaners.rsc" dst-path=scaners.rsc check-certificate=yes]
:delay 10s
:if ([/file find name="scaners.rsc"] != "") do={
/ip firewall address-list remove [find list="scaners"]
:delay 2s
/imp scaners.rsc
:delay 5s
/file remove [find name="scaners.rsc"]
:log warning "扫描者黑名单更新完成"}
#!/bin/sh
PATH=$PATH:/sbin:/bin:/usr/sbin:/usr/bin
wget -q -O /root/upfw.bak https://cache-1.oss-cn-beijing.aliyuncs.com/file/scaners.bak
sleep 10s
iptables -F
sleep 5s
iptables-restore </root/upfw.bak
sleep 5s
rm /root/upfw.bak
mikrotik设备(import导入):https://cache-1.oss-cn-beijing.aliyuncs.com/file/scaners.rsc
linux设备(iptables-restore导入):https://cache-1.oss-cn-beijing.aliyuncs.com/file/scaners.bak
 oss-cn-beijing-aliyuncs-com-chain.pem.txt (下载后将TXT去掉)
oss-cn-beijing-aliyuncs-com-chain.pem.txt (下载后将TXT去掉)
 scaners.rsc.txt (下载后将TXT去掉)
scaners.rsc.txt (下载后将TXT去掉)
转自大猫猫
留言评论
暂无留言